A Verkle tree is a dedication scheme that works much like a Merkle tree, however has a lot smaller witnesses. It really works by changing the hashes in a Merkle tree with a vector dedication, which makes wider branching components extra environment friendly.
Due to Kevaundray Wedderburn for suggestions on the publish.
Overview
For particulars on how verkle timber work, see:
The intention of this publish is to elucidate the concrete format of the draft verkle tree EIP. It’s geared toward consumer builders who wish to implement verkle timber and are on the lookout for an introduction earlier than delving deeper into the EIP.
Verkle timber introduce plenty of modifications to the tree construction. Essentially the most vital modifications are:
- a swap from 20 byte keys to 32 byte keys (to not be confused with 32 byte addresses, which is a separate change);
- the merge of the account and storage tries; and eventually
- The introduction of the verkle trie itself, which makes use of vector commitments as an alternative of hashes.
Because the vector dedication scheme for the verkle tree, we use Pedersen commitments. Pedersen commitments are primarily based on elliptic curves. For an introduction to Pedersen commitments and the way to use them as polynomial or vector commitments utilizing Internal Product Argumentss, see here.
The curve we’re utilizing is Bandersnatch. This curve was chosen as a result of it’s performant, and in addition as a result of it is going to permit environment friendly SNARKs in BLS12_381 to cause in regards to the verkle tree sooner or later. This may be helpful for rollups in addition to permitting an improve the place all witnesses will be compressed into one SNARK as soon as that turns into sensible, with no need an extra dedication replace.
The curve order/scalar area measurement of bandersnatch is p = 13108968793781547619861935127046491459309155893440570251786403306729687672801, which is a 253 bit prime. Because of this, we are able to solely safely decide to bit strings of at most 252 bits, in any other case the sphere overflows. We selected a branching issue (width) of 256 for the verkle tree, which suggests every dedication can decide to as much as 256 values of 252 bits every (or to be exact, integers as much as p – 1). We write this as Commit(v₀, v₁, …, v₂₅₅) to decide to the record v of size 256.
Format of the verkle tree
One of many design targets with the verkle tree EIP is to make accesses to neighbouring positions (e.g. storage with virtually the identical handle or neighbouring code chunks) low cost to entry. With a purpose to do that, a key consists of a stem of 31 bytes and a suffix of 1 byte for a complete of 32 bytes. The important thing scheme is designed in order that “shut” storage places are mapped to the identical stem and a unique suffix. For particulars please take a look at the EIP draft.
The verkle tree itself is then composed of two kinds of nodes:
- Extension nodes, that signify 256 values with the identical stem however totally different suffixes
- Internal nodes, which have as much as 256 youngsters, which will be both different internal nodes or extension nodes.
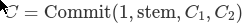
The dedication to an extension node is a dedication to a 4 aspect vector; the remaining positions will probably be 0. It’s:
C₁ and C₂ are two additional commitments that decide to all of the values with stem equal to stem. The explanation we want two commitments is that values have 32 bytes, however we are able to solely retailer 252 bits per area aspect. A single dedication would thus not be sufficient to retailer 256 values. So as an alternative C₁ shops the values for suffix 0 to 127, and C₂ shops 128 to 255, the place the values are break up in two with the intention to match into the sphere measurement (we’ll come to that later.)
The extension along with the commitments C₁ and C₂ are known as “extension-and-suffix tree” (EaS for brief).
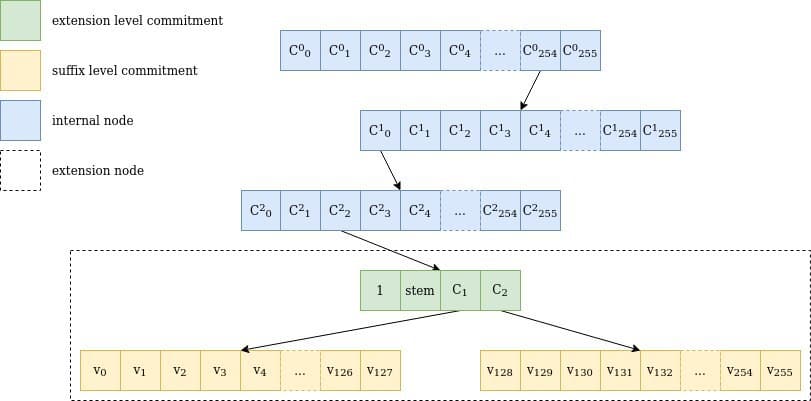
Determine 1 Illustration of a stroll by means of a verkle tree for the important thing 0xfe0002abcd..ff04: the trail goes by means of 3 inner nodes with 256 youngsters every (254, 0, 2), one extension node representing abcd..ff and the 2 suffix tree commitments, together with the worth for 04, v₄. Be aware that stem is definitely the primary 31 bytes of the important thing, together with the trail by means of the interior nodes.
Dedication to the values leaf nodes
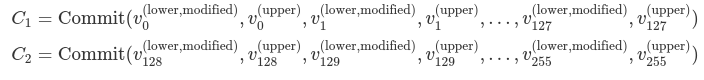
Every extension and suffix tree node comprises 256 values. As a result of a worth is 256 bits broad, and we are able to solely retailer 252 bits safely in a single area aspect, 4 bits could be misplaced if we merely tried so retailer one worth in a single area aspect.
To avoid this drawback, we selected to partition the group of 256 values into two teams of 128 values every. Every 32-byte worth in a bunch is break up into two 16-byte values. So a worth vᵢ∈ 𝔹₃₂ is become v⁽ˡᵒʷᵉʳ⁾ᵢ ∈ 𝔹₁₆ and v⁽ᵘᵖᵖᵉʳ⁾ᵢ∈ 𝔹₁₆ such that v⁽ˡᵒʷᵉʳ⁾ᵢ ++ v⁽ᵘᵖᵖᵉʳ⁾ᵢ= vᵢ.
A “leaf marker” is added to the v⁽ˡᵒʷᵉʳ⁾ᵢ, to distinguish between a leaf that has by no means been accessed and a leaf that has been overwritten with 0s. No worth ever will get deleted from a verkle tree. That is wanted for upcoming state expiry schemes. That marker is about on the 129th bit, i.e. v⁽ˡᵒʷᵉʳ ᵐᵒᵈⁱᶠⁱᵉᵈ⁾ᵢ = v⁽ˡᵒʷᵉʳ⁾ᵢ + 2¹²⁸ if vᵢ has been accessed earlier than, and v⁽ˡᵒʷᵉʳ ᵐᵒᵈⁱᶠⁱᵉᵈ⁾ᵢ = 0 if vᵢ has by no means been accessed.
The 2 commitments C₁ and C₂ are then outlined as
Dedication of extension nodes
The dedication to an extension node consists of an “extension marker”, which is simply the number one, the 2 subtree commitments C₁ and C₂, and the stem of the important thing resulting in this extension node.
Not like extension nodes within the Merkle-Patricia tree, which solely comprise the part of the important thing that bridges the mum or dad inner node to the kid inner node, the stem covers the entire key as much as that time. It’s because verkle timber are designed with stateless proofs in thoughts: if a brand new secret is inserted that “splits” the extension in two, the older sibling needn’t be up to date, which permits for a smaller proof.
Dedication of Inner nodes
Inner nodes have the less complicated calculation technique for his or her commitments: the node is seen as a vector of 256 values, which can be the (area illustration of the) root dedication of every of their 256 subtrees. The dedication for an empty subtree is 0. If the subtree is just not empty, then the dedication for the interior node is
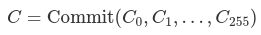
the place the Cᵢ are the youngsters of the interior node, and 0 if a toddler is empty.
Insertion into the tree
Determine 2 is an illustration of the method of inserting a brand new worth into the tree, which will get fascinating when the stems collide on a number of preliminary bytes.
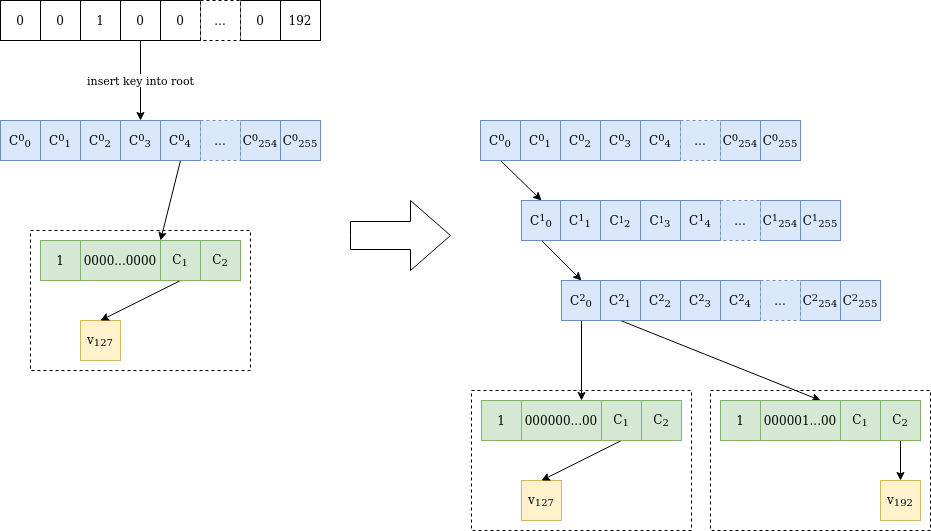
Determine 2 Worth v₁₉₂ is inserted at location 0000010000…0000 in a verkle tree containing solely worth v₁₂₇ at location 0000000000…0000. As a result of the stems differ on the third byte, two inner nodes are added till the differing byte. Then one other “extension-and-suffix” tree is inserted, with a full 31-byte stem. The preliminary node is untouched, and C²₀ has the identical worth as C⁰₀ earlier than the insertion.
Shallower timber, smaller proofs
The verkle tree construction makes for shallower timber, which reduces the quantity of saved information. Its actual energy, nonetheless, comes from the flexibility to provide smaller proofs, i.e. witnesses. This will probably be defined within the subsequent article.
